
Microsoft is tracking a series of attacks that use SEO poisoning to infect targets with a remote access trojan (RAT) capable of stealing the victims' sensitive info and backdooring their systems.
The malware delivered in this campaign is SolarMarker (aka Jupyter, Polazert, and Yellow Cockatoo), a .NET RAT that runs in memory and is used by attackers to drop other payloads on infected devices.
SolarMarker is designed to provide its masters with a backdoor to compromised systems and steal credentials from web browsers.
The data it manages to harvest from infected systems is exfiltrated to the command-and-control server. It will also gain persistence by adding itself to the Startup folder and modifying shortcuts on the victims' desktop.
In April, eSentire researchers observed threat actors behind SolarMaker flooding search results with over 100,000 web pages claiming to provide free office forms (e.g., invoices, questionnaires, receipts, and resumes).
However, they would instead act as traps for business professionals searching for document templates and infect them with the SolarMaker RAT using drive-by downloads and search redirection via Shopify and Google Sites.
Switches to abuse AWS and Strikingly
In more recent attacks spotted by Microsoft, the attackers have switched to keyword-stuffed documents hosted on AWS and Strikingly, and are now targeting other sectors, including finance and education.
"They use thousands of PDF documents stuffed w/ SEO keywords and links that start a chain of redirections eventually leading to the malware," Microsoft said.
"The attack works by using PDF documents designed to rank on search results. To achieve this, attackers padded these documents with >10 pages of keywords on a wide range of topics, from 'insurance form' and 'acceptance of contract' to 'how to join in SQL' and 'math answers'."
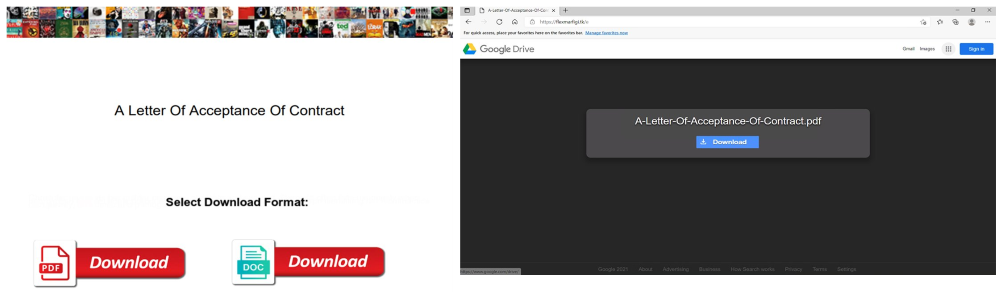
Once the victims find one of the maliciously crafted PDFs and open them, they are prompted to download another PDF or DOC document containing the information they are looking for.
Instead of gaining access to the info, they are redirected through multiple websites using .site, .tk, and .ga TLDs to a cloned Google Drive web page where they are served the last payload, the SolarMaker malware.
The SolarMaker developers are believed to be Russian-speaking threat actors based on Russian to English translation misspelling, according to Morphisec.
The Morphisec researchers also found that many of the malware's C2 servers are located in Russia, although many were no longer active.
"The TRU has not yet observed actions-on-objectives following a SolarMarker infection, but suspect any number of possibilities, including ransomware, credential theft, fraud, or as a foothold into the victim networks for espionage or exfiltration operations," eSentire’s Threat Response Unit (TRU) added.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now